[dfads params=’groups=-1′]
While researching through website traffic problems, the first thing that came in my mind is DoS / DDoS attacks. So, I started to study about it.
What is DoS / DDoS attack?
(Wiki Answer) : In computing, a denial-of-service attack (DoS attack) or distributed denial-of-service attack (DDoS attack) is an attempt to make a machine or network resource unavailable to its intended users. Although the means to carry out, motives for, and targets of a DoS attack may vary, it generally consists of efforts to temporarily or indefinitely interrupt or suspend services of a host connected to the Internet.
How to check if your Linux server is under DDOS Attack?
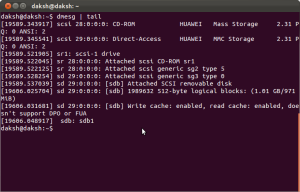
Login to your Linux Server and type the following command:
netstat -anp |grep ‘tcp\|udp’ | awk ‘{print $5}’ | cut -d: -f1 | sort | uniq -c | sort –n
This command will show you the list of IP’s which have logged in is maximum number of connections to your server. It becomes more complex if the attacker use fewer connections with more number of attacking IP’s.
[dfads params=’groups=-1′]
We can check active connections to the server using the following command:
netstat -n | grep :80 |wc –l
The above command will show the active connections that are open to your server. The result may vary but if it shows connections more than 500, then you will be definitely having problems.
netstat -n | grep :80 | grep SYN |wc –l
If the result of the above command is 100 or above then you are having problems with sync attack.
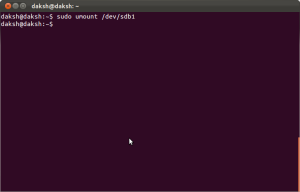
Once you get an idea of the ip attacking your server, you can easily block it. Fire the following command to block specific IP:
route add ipaddress reject
Fire the following command to check whether that IP is blocked or not:
route -n |grep IPaddress
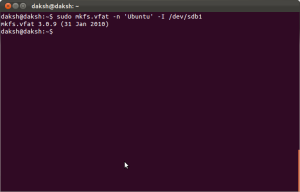
You can also block a IP with iptables on the server by using the following command.
iptables -A INPUT 1 -s IPADRESS -j DROP/REJECT
service iptables restart
service iptables save
After firing the above command, KILL all httpd connection and than restart httpd service by using following command:
killall -KILL httpd/apache2
[dfads params=’groups=-1′]
[Updated 12-12-2013]
In order to delete the route entry, fire the following command.
ip route delete ipaddress
[Source : https://kb.hivelocity.net/how-to-check-if-your-linux-server-is-under-ddos-attack/]